Leave IT To Us.
San Antonio’s Managed Service Provider
Dependable expertise that helps you achieve your business goals.
MSP Experts You Can Count On
Our highly trained engineers deliver comprehensive IT support solutions that keep your unique business running optimally. Look no further. We are your managed service provider in San Antonio.
Government Certifications
We’ve completed the requirements to bid on government projects and are GSA certified.

GSA Schedule 70: Multiple Award Contract #47QTCA18D00AE

SCTRCA: South Central Texas Regional Certification Agency: Enterprise
MBE: Minority Business Enterprise
ESBE: Emerging Small Business Enterprise
HABE: Hispanic American Business
SBE: Small Business Enterprise
CHSE: Certified HIPAA Security Expert
Partners












Industries
Your success is how we measure our success. At Salco, we serve these industries:
Construction
Hit deadlines and enjoy smoother project completion with our services and solutions.
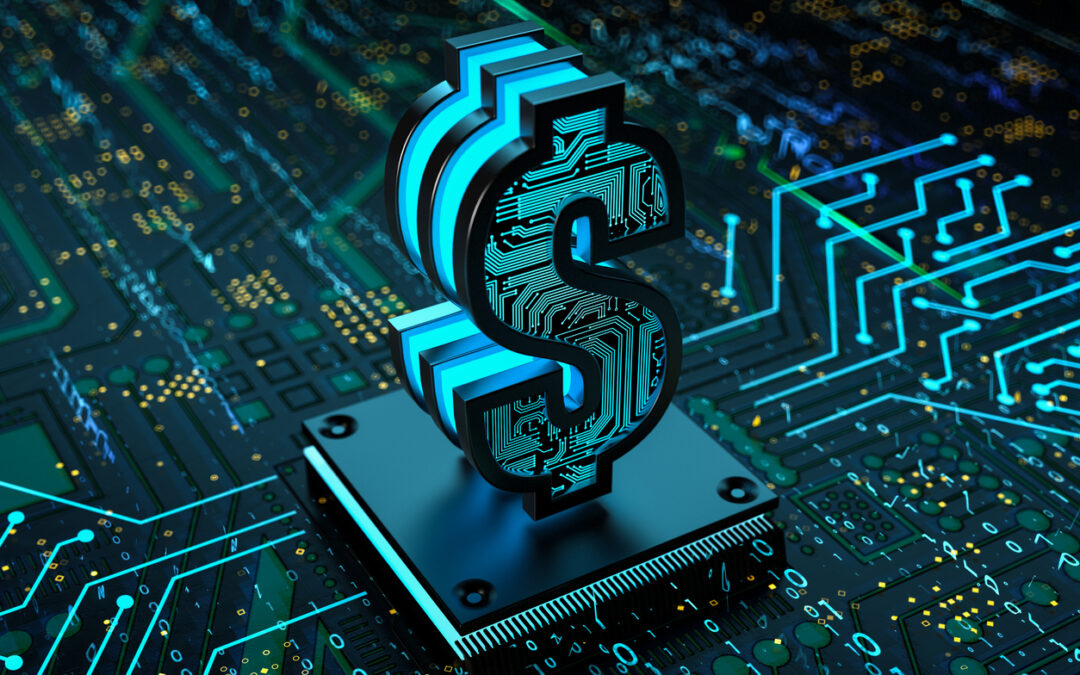
Finance
We deliver IT solutions and strategies that financial organizations depend on.
Healthcare
Your practice runs smoothly with HIPAA-compliant, 24/7 IT support.

Legal
Leverage technology to help your firm’s plans align with your goals.

Logistics
Our team of professionals optimizes the efficiencies of your business.
Oil & Gas
Leverage IT solutions to enhance efficiencies in a demanding environment.
Nonprofit
Make more impacts with scalable, cost-effective solutions and improved operations.

Logistics
Our team of professionals optimizes the efficiencies of your business.
Oil & Gas
Leverage IT solutions to enhance efficiencies in a demanding environment.
Nonprofit
Make more impacts with scalable, cost-effective solutions and improved operations.
Check Out Our Tech Blogs
Partner with Us
Your IT solutions are our business. Let us manage your IT, so you can manage your business.